What is Screening in KYC?
KYC, or know your client, is a set of measures that are implemented in order to tell the difference between favorable and unfavorable clients, specifically those with criminal or political connections, criminal records, or any history that otherwise deems them to be a high-risk customer.
Performing KYC screening has historically been tedious and unreliable since there are so many variables that affect the reliability score of each customer. Despite this, banks, financial institutions all over the world are forced to perform KYC screening over the last couple of decades as the act of lending money to a person or a business is a high-risk activity, and lending money to someone with a high risk of bankruptcy, or someone who might be involved in criminal activity, can be really damaging to any financial institution.
Nowadays many other industries face the same reality and are now implementing KYC compliance measures. For example, with the rise of online services - from car and apartment renting to online freelance platforms - the question of safe client onboarding has become more important than ever. Unfortunately, KYC compliance is still a complicated subject for many businesses, leaving them unsure how to acquire, collate and analyze client information.
It is the responsibility of each business to ensure KYC compliance, including properly documenting and keeping relevant records of clients’ data, screening new clients, checking their finance and legal history, checking document legibility, etc. Failure to do so brings significant risks in terms of financial cost, damage to reputation, and potential legal consequences.
At a minimum, there are three primary objectives when gathering KYC information:
- identify the customer - mainly through the documents provided by the clients, like an ID, a deriver’s license, etc.
- verify the customer’s identity - using traditional or AI methods, like facial recognition
- store the customer information for future screening, e.g. multi-account screening
While each step can be made using traditional methods, like manual client screening and manual document processing, it is not a feasible long-term approach for any business which values speed, efficiency, and scalability. It is also important your KYC screening operations are reliable and are free from human mistake factors.
The Limitations of KYC Screening
While screening your customers is an important step for risk assessment, it is not the only tool that should be used. The limitations of screening are that in general it only brings up details of those clients who have already been marked as ‘unfavorable’ due to their past actions and history. But many previously untainted clients might still turn out to be high-risk, abusing your platform in some way or committing money laundering.
Types of KYC screening
There are multiple types of screening a business can conduct, which involve sanctions screening, politically exposed person screening, financial fraud screening, and legal screening. Looking at KYC screening from a more practical point of view, the screening procedures can be divided into two types:
Document screening
Documents provided by the client during onboarding need to be properly scanned and processed so that the information can later be used for screening. Processing of documents can be automated easily using OCR methods.
Biometric screening
One of the key aspects of KYC screening is the process of identity verification. The most effective way to verify identity and store client information for further screening is via biometric verification like facial recognition. Using AI for identity verification is the quickest and most fail-proof way to screen clients.


How to Upgrade Your KYC Screening Processes
The KYC screening process can become labor-intensive once you receive the data. It can seem even more daunting if all screening processes are done manually, including document processing. Automation of key screening processes can significantly cut down on processing time and reduce human error while improving client satisfaction through a better user experience. Automating KYC screening is beneficial for both parties involved since automation reduces the onboarding time, making joining your service a lot easier.
Identity the screening information
Before starting the KYC upgrading process, you need to first identify which information you already use or plan on using for client screening. The range of information can vary greatly across different businesses, for example, setting up a bank account to receive a loan requires a higher level of customer screening than joining an online freelance platform.
Outlining what information you will need for screening ahead of time can help reduce the time needed for KYC updates and create the most effective screening process. The information may include client ID, driver’s license, client photos, etc.
Decide how you will collect information
This is an important step in the process of upgrading your KYC screening processes as it will affect the way the entire screening system will operate:
- in-person information collection - each client will have to visit your office for you to collect their information
In this case, the system would have to be set up with your employees in mind as they will be the ones who will operate it. This way of information collection also means you will have to have screening personnel, which is not a problem for those with an established screening process and a problem for those without.
- remote information collection - the client provides all the information themselves remotely (using a mobile app or a web client)
The remote approach to data collection seems the most promising - with more and more businesses embracing the transition to online operations and more people discovering how convenient remote services can be, both you and your client are more likely to reap the most benefits from introducing remote KYC screening. The information required for KYC screening can be submitted by the client using a mobile app or a website without ever leaving their house, making your services even more attractive to use, while smart automation powered by artificial intelligence will improve your KYC screening and assess risks with high accuracy.

Decide how you will identify the customer
Document fraud is rampant, especially since most businesses have embraced ‘the online’ - it has become relatively easy to submit someone elses’ document during the registration process. In addition, identifying your customer is important for additional screening and storing information.
In-person KYC screening makes identification relatively easy - comparing a person and their ID photo is something we are all used to. This method, however, leaves out identical twins and various cosmetic procedures a person can go through to change their appearance, as well as leaves room for the human factor.
Remote, ‘self-submitted’ identity verification is the most failproof and effective method of making sure your clients provide the right documents. Remote identity verification requires the introduction of artificial intelligence in the form of facial recognition to compare the person to their ID and check their identity against various databases.
Facial recognition can be easily implemented into a mobile app so that your clients can simply use their smartphone camera to do through the screening process in a matter of minutes, while you receive not only the document information but a facial profile of all your clients - highly useful for further in-depth screening especially relevant for financial institutions.
Choose your screening platform
As with any software, you need to choose the platform - either offline software, a web client, or a mobile app. For large businesses, it makes sense to introduce multiple platforms to create a cohesive ecosystem easy to use for both your clients and employees. As many businesses already have a mobile app for their clients, the easiest step is to introduce KYC screening into an existing app.
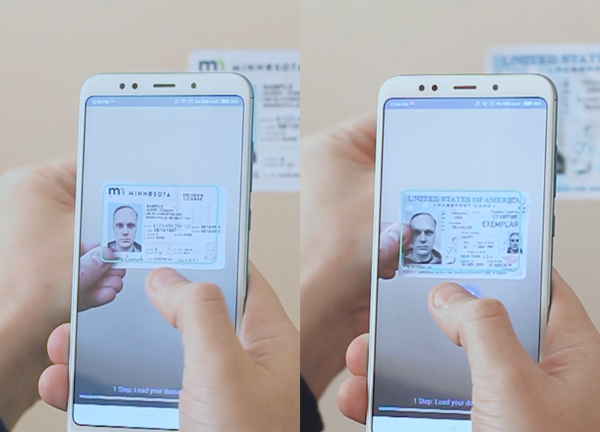
The mobile app can also be used to scan documents and automatically process them. Instead of your employees filling out client information by hand, your clients can snap a quick photo of their ID and the app will do the rest - detect all relevant information (ID number, client name, etc.) and automatically process the data by uploading it to your databases, filling in relevant forms, etc.
Next Steps: Ongoing Monitoring
KYC screening is not a ‘one and done’ deal - it is an ongoing process. Checking up on your client information often will keep the information up to date, as well as check if the risk status of the client has changed over time.
Multi Accounting Fraud
Another concern is multi-accounts - a situation when one person creates multiple accounts using different documents to abuse your services. A basic level of multi-accounting would be a user creating multiple accounts using multiple email addresses.

More sophisticated cases would see fraudsters using emulators, virtual machines, proxies, or mobile networks to leverage fresh IP addresses, as well as using stolen data or synthetic identities.
Industries impacted by multi-accounting fraud
Loan providers are among the most affected by multi-accounting fraud as fraudsters use multi-accounting to default on the loan and run away with the money, as well as get access to payment methods for fraudulent purposes.
Online dating, eCommerce, and the travel industry are also greatly affected by this type of fraud. Multiple accounts can be used to spam the users of the service, leave scammer reviews to damage the business’ reputation, spam discount codes, and offers at scale.
Solutions to Multi Accounting Fraud
The immediate reaction to combating multi-accounting fraud is to implement more steps during the onboarding process to eliminate fraudsters from the get-go.
However, this may cause more friction to the user experience for real clients, and not be entirely effective against the problem at hand. One of the best ways to combat multi-accounting fraud is to implement facial recognition so that each account is associated with a real face.
Facial recognition algorithms are notoriously difficult to fool, they work well even with identical twins, and can be easily implemented into a mobile app. If a person will attempt to create a second account using fake, stolen, or synthesized data, the facial recognition algorithm will detect the multi-accounting attempt and prohibit the user from proceeding.
How you can use AI to automate KYC screening
KYC screening can be complex, time-consuming, and intimidating at first, but as you break down your screening operations into individual steps, outline how and where the screening will take place, it becomes much more manageable.
While creating a strong KYC screening process is possible without using modern technology advances by hiring more employees, setting up visiting times for your clients to come in and submit their paperwork, dedicating a research team to look up the client’s past history, checking document validity, check for impersonation and multi-account fraud.
However, creating a large team dedicated to client screening may not be feasible - or practical - for many businesses, while screening still remains an important objective. In addition, the traditional way of KYC screening is time-consuming and highly prone to mistakes as the sheer amount of information needed to be analyzed provides ample room for human error.
One of the best ways to implement modern KYC screening is by developing an AI-powered system for quick and effective screening. AI algorithms now are extremely reliable and can process complex data in a matter of minutes. With the use of AI, screening clients can become as easy as turning on a frontal camera.
Facial Recognition for KYC screening
AI algorithms can detect a human face and compare it to those saved in a database, detecting if a person is included in a list of unreliable clients or if a person already has an account.
The introduction of facial recognition into KYC screening eliminates multi-account fraud as the algorithms will detect duplicate accounts during the onboarding, saving a lot of time in the process - facial detection checks happen almost instantaneously.
An AI system can quickly look through all available databases to find a match for a face it has just scanned and find any needed background information on the person.
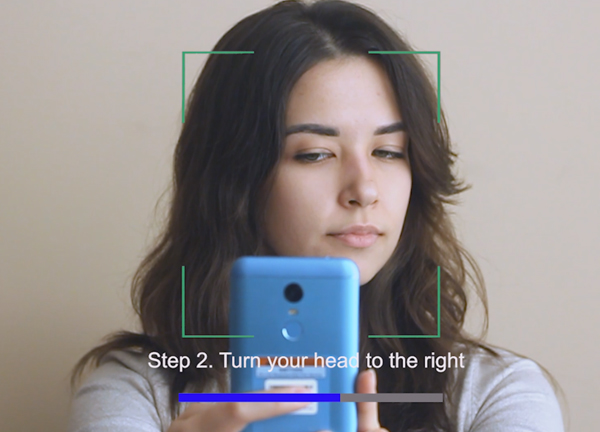
Liveness Detection
Facial recognition can also help with liveness detection. Attempts at impersonation, such as image and video spoofing, deepfakes, etc. can all be recognized using AI. During the registration process, your client can be asked to perform a series of simple facial gestures, such as winking, smiling, and head-turning in order to detect facial liveness. This eliminates many types of fraud while being easy to use for your clients.
Image spoofing can be one of the ways unreliable clients may try to fool a facial detection system. In short, image spoofing is a process during which a person, instead of showing their own face, shows an image of a different person in an attempt to steal their identity - or hide their own.
Another way in which some may try to get around your KYC screening is by showing a video of a different person or a deepfake. While it may look convincing to a human eye, a facial recognition algorithm is much harder to fool. An AI-powered system can easily identify if the person in front of the camera is real or is it just a photo or a video of them.
Automated Document Recognition
Instead of manually checking if a document is fake or forged, you can use AI to check it for you. Documents can be scanned using a camera on a client’s smartphone, and AI will do the rest - recognize document type, number, and all relevant information, automatically fill out any forms and check for any signs of a forged document.
Not only will automatic document scanning increase the reliability of your KYC screening, but it will also make your service more user-friendly - nobody likes typing all of their personal information by hand.
Best Ways To Implement AI Into KYC Screening
The easiest, most user-friendly way to incorporate all of the best KYC screening practices powered by AI into your business is through a mobile app. In the modern-day, all businesses have some sort of an online presence, and many already have an app. Including an AI-powered screening module into an existing app can increase the effectiveness of your KYC screening dramatically, as well as make your services more appealing to your customers.
All data input - document scanning, facial recognition - can be done using a smartphone’s camera.
FAQs
How Do You Implement Intelligent KYC Screening
Implementation of intelligent KYC required the implementation of intelligent software, often involving document recognition, facial identification, liveness detection, and other forms of AI. The best way to implement intelligent KYC screening is through an AI-powered mobile app.
What is biometric KYC?
Biometric KYC is any practice of identifying your client using their biometric data, such as fingerprints, face, etc. In most cases, biometric KYC screening using facial recognition is the most practical approach - both from the ease of implementation standpoint and accuracy standpoint.
How Does Facial Recognition Confirm Identity?
Facial detection algorithms can scan a photo present on a submitted document, like an ID, and compare it to a person in front of the camera, confirming the identity. Facial recognition can also be used to look through databases and find matches to detect fraudsters or otherwise unreliable clients.
